Imagine you own a very expensive, high-performance sports car. You park it in a public lot. Would you leave the doors unlocked and the keys in the ignition? Of course not. If you did, anyone could jump in, drive it recklessly, use up your gas, and potentially crash it.
In the world of software development, a powerful voice infrastructure is that sports car. It has the power to make thousands of calls, stream audio globally, and process complex AI conversations.
The AI Voice API key is your set of keys to that car.
When developers build applications using a Software Development Kit (SDK), they are connecting their code to a massive, expensive backend infrastructure. This connection needs to be secure. Without a proper locking mechanism, unauthorized users could hijack the system, make fraudulent calls on your dime, or access private data.
In this guide, we will explore why these keys are the cornerstone of modern software security. We will look at how they enable dynamic call setup API functionalities, how they protect your budget, and how platforms like FreJun AI use them to ensure that your configurable voice AI remains safe and under your control.
Table of contents
- What Is an AI Voice API Key?
- Why Is Security So Critical in Voice Infrastructure?
- How Does the Key Enable Dynamic Call Setup?
- What Are Runtime Parameters?
- How Does FreJun AI Secure Your Connection?
- What Is Configurable Voice AI?
- How Do API Keys Help with Usage Tracking?
- What Happens If You Lose Your Key?
- Best Practices for Managing Your Keys
- How Does Infrastructure Impact API Security?
- The Role of Rate Limiting
- Why Enterprises Prefer Key-Based Authentication
- Conclusion
- Frequently Asked Questions (FAQs)
What Is an AI Voice API Key?
At its simplest level, an AI Voice API key is a unique string of characters. It looks like a long, random password. It is generated by the service provider and given to the developer.
This key serves two main purposes:
- Authentication: It tells the server “I am who I say I am.”
- Authorization: It tells the server “I am allowed to do these specific things.”
When your application sends a request to the FreJun infrastructure—for example, to start a phone call—it includes this key in the header of the message. Our servers check the key against our database. If it matches, the gate opens. If it does not, the gate stays shut.
Think of it like a digital passport. You cannot enter a foreign country without showing your passport at the border. Similarly, your code cannot enter the voice network without showing its API key.
Why Is Security So Critical in Voice Infrastructure?
You might wonder why we need such strict security. Why not just let anyone use the API?
The answer lies in the nature of telephony. Unlike a free weather app API, voice APIs cost money to operate. Every minute of a phone call incurs carrier fees. Every minute of AI processing incurs compute costs.
If a hacker steals your API key, they can commit “toll fraud.” This is where bad actors use your account to pump traffic to expensive premium-rate phone numbers that they own. They make money, and you get stuck with a massive bill.
According to a report by the Communications Fraud Control Association (CFCA), global telecom fraud loss is estimated to be over $38 billion annually. A significant portion of this comes from compromised accounts and API keys.
By enforcing strict API key requirements, platforms like FreJun protect you from becoming a statistic. The key ensures that only your authorized applications can trigger billing events.
Also Read: Future-Focused Voice Recognition SDK for Rapid Innovation
How Does the Key Enable Dynamic Call Setup?
Modern voice applications are not static. They change behavior based on who is calling and why. This flexibility is powered by a dynamic call setup API.
When you initiate a session using the FreJun SDK, you pass your API key along with a set of instructions. These instructions tell the infrastructure how to handle the call right now.
For example, you might want to:
- Record this specific call but not the next one.
- Use a female voice for this customer and a male voice for the next.
- Route the audio to a specific AI model based on the user’s language.
The API key validates your right to send these instructions. Once validated, the system accepts your runtime parameters. These are the variables that change from call to call. Without the secure handshake provided by the key, the system would reject these dynamic commands to prevent malicious manipulation.
What Are Runtime Parameters?
Runtime parameters are the specific details you feed into the system at the moment the software runs. In the context of voice, this includes things like:
- To_Number: The person you are calling.
- From_Number: The Caller ID you want to show.
- Webhook_URL: Where you want call events sent.
- AI_Model_ID: Which brain should power the conversation.
Your AI Voice API key acts as the master signature that signs off on these parameters. It confirms that you authorized the system to call that specific number using that specific AI model.
Here is a simple table showing the difference between static and dynamic setups enabled by secure keys.
| Feature | Static Setup (No Runtime Control) | Dynamic Call Setup (With API Key) |
| Routing | Calls always go to the same place | Calls route based on live logic |
| Configuration | Settings are hardcoded | Settings change via runtime parameters |
| Security | Rigid and often insecure | Validated per request |
| Flexibility | Low | High (infinite variation) |
| Updates | Requires code deployment | Updates instantly via API |
How Does FreJun AI Secure Your Connection?
FreJun AI takes security seriously because we handle the mission-critical voice layer for businesses. We handle the complex voice infrastructure so you can focus on building your AI.
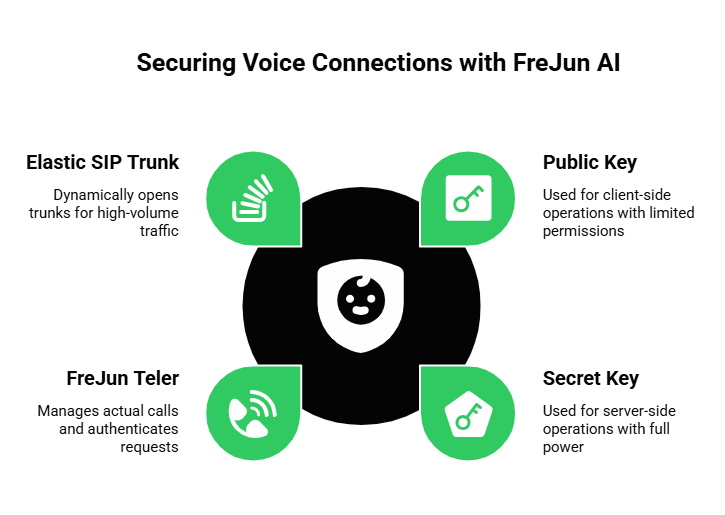
When you sign up for FreJun, you receive a pair of keys: a Public Key and a Secret Key.
- Public Key: Used for client-side operations (like a web browser phone). It has limited permissions.
- Secret Key: Used for server-side operations. It has full power to buy numbers, create SIP trunks, and manage billing.
We utilize FreJun Teler, our telephony infrastructure arm, to manage the actual calls. When your application requests a call via Teler, we check your Secret Key. If it is valid, we open an elastic SIP trunk dynamically. This ensures that your high-volume traffic is authenticated instantly, preventing unauthorized access to our global carrier network.
What Is Configurable Voice AI?
One of the main benefits of using an API is that it makes your voice agent configurable. Configurable voice AI means you can tweak the personality, speed, and behavior of the voice without rewriting your entire application.
The API key links your code to your configuration dashboard.
Imagine you want to change your AI’s greeting from “Hello” to “Good Morning.” You do not want to redeploy your app just for that. Instead, you update the configuration in your database. When your app initializes the call, it pulls this new config and passes it as a runtime parameter, authenticated by your API key.
This separation of code and configuration allows businesses to iterate faster. Marketing teams can update scripts while developers focus on stability, all held together by the secure access the API key provides.
Also Read: Voice Recognition SDK Built for Modern Digital Platforms
How Do API Keys Help with Usage Tracking?
Beyond security, keys are vital for analytics. Every time your key is used, we log the activity.
This allows you to see:
- How many calls did we make today?
- Which specific application features are being used most?
- Are we approaching our budget limit?
This data is crucial for configurable voice AI optimization. If you see that calls using a certain AI model are costing 20% more but lasting 50% longer, you might decide to switch models. The API key is the identifier that tags every single data point to your account, giving you granular visibility into your operations.
According to data, API attacks have increased by 400% in recent years. This statistic highlights why robust usage tracking and anomaly detection, powered by unique API keys, are essential for spotting weird behavior before it becomes a problem.
What Happens If You Lose Your Key?
Because your Secret Key is so powerful, losing it is a problem. It is like losing the master key to your office building.
However, API keys offer a solution called “rotation.”
If you suspect your key has been leaked (maybe a developer accidentally posted it on GitHub), you can log into your FreJun dashboard and “roll” the key. This process deletes the old key and generates a brand new one.
Instantly, the old key stops working. Anyone trying to use it will get a “401 Unauthorized” error. You then update your secure server with the new key. This ability to revoke access instantly is a massive security advantage over traditional username/password systems which are often shared and harder to reset across multiple services.
Best Practices for Managing Your Keys
To keep your dynamic call setup API secure, follow these golden rules:
- Never Commit to Git: Do not write your key directly in your code files. If you upload that code to a public repository, hackers will scrape it in seconds.
- Use Environment Variables: Store keys in a separate .env file on your server. Your code should read the key from there.
- Restrict Permissions: If possible, use keys that only have permission to do what is necessary. Do not give an administrative key to a junior developer’s testing app.
- Rotate Regularly: Change your keys every few months just to be safe.
How Does Infrastructure Impact API Security?
The key protects the door, but the walls need to be strong too.
FreJun AI provides a secure transport layer. When you send your API key to us, it travels over an encrypted HTTPS connection. This means no one can intercept it while it is moving across the internet.
Furthermore, FreJun Teler ensures that the voice media itself is secure. We use protocols like SRTP (Secure Real-time Transport Protocol) to encrypt the audio packets. This prevents “eavesdropping,” where a bad actor tries to listen in on the call. The API key is the first step in a chain of security measures that protects your business from end to end.
Ready to build secure and scalable voice applications? Sign up for FreJun AI to generate your secure API keys today.
The Role of Rate Limiting
Another security feature tied to your API key is “rate limiting.”
Imagine a bug in your code causes your app to try and dial one million calls in one second. This would crash your system and drain your wallet.
Because we identify you by your API key, FreJun can set safety limits. We can say, “This key is allowed to make 10 calls per second.” If you try to make 100, we block the extra 90 and send you an error message.
This acts as a circuit breaker. It protects you from your own mistakes and protects our infrastructure from being overwhelmed. It ensures stable service for everyone.
Also Read: How a Voice API for Bulk Calling Streamlines Customer Updates?
Why Enterprises Prefer Key-Based Authentication
Enterprises love API keys because they integrate easily with automated systems.
In a large company, you might have fifty different servers running your voice application. You cannot have a human logging in with a password on every server every day.
API keys are designed for machine-to-machine communication. Your servers can talk to FreJun’s servers automatically, 24/7, without human intervention. This automation is what allows for massive scale. Whether you are sending one call or one million, the key enables the dynamic call setup API to function smoothly and securely without anyone lifting a finger.
Conclusion
The AI Voice API key is not just a random string of text. It is the guardian of your voice infrastructure. It stands between your bank account and the chaos of the open internet.
By requiring a key for SDK access, platforms ensure that every call is authenticated, authorized, and tracked. This enables powerful features like dynamic call setup API, allowing you to change runtime parameters on the fly. It allows for configurable voice AI that can adapt to any user need.
Most importantly, it provides peace of mind. It allows you to build innovative voice applications knowing that the expensive and powerful engine underneath is locked, secure, and only responding to your commands.
FreJun AI is built on this foundation of security. With FreJun Teler handling the global telephony and our secure API handling the access control, you can deploy enterprise-grade voice agents with confidence. We provide the keys, the car, and the road; you just have to drive.
Want to learn more about our security features and infrastructure? Schedule a demo with our team at FreJun Teler and let us show you how to build a safe and powerful voice stack.
Also Read: United Kingdom Country Code Explained
Frequently Asked Questions (FAQs)
It is a unique security credential (a long string of characters) used to authenticate your application when it communicates with a voice provider’s API. It acts like a password for your software.
You typically find it in the developer dashboard of your service provider. After you sign up for FreJun, your keys will be visible in the “Settings” or “API Credentials” section.
You should never share your Secret Key with anyone outside your trusted team. If you need to give access to a contractor or partner, generate a specific key for them with limited permissions, or rotate it after they are done.
These are the data points you send to the API at the exact moment you start a call. Examples include the phone number to dial, the caller ID to display, and the specific AI model to use for that conversation.
The key ensures that only authorized code can initiate billing events (like phone calls). Without the key, hackers cannot use your account to make expensive calls to premium numbers.
It refers to the ability to change how your voice agent sounds and behaves (e.g., tone, language, speed) by changing settings in the software, authorized by the API key, rather than rewriting the core code.
They are similar, but an API Key is designed for software-to-software communication, whereas a password is designed for human-to-software login. API keys are usually longer and more complex.
You should revoke it immediately. Go to your provider’s dashboard and “rotate” or regenerate the key. This will stop the old key from working and prevent anyone from using it.