In the modern, data-driven enterprise, the voice call is no longer just a conversation; it is a rich and often highly sensitive stream of data. From a patient discussing their medical history with an AI-powered healthcare agent, to a financial advisor confirming a major trade with a client, to a board meeting discussing confidential strategy, the audio stream of a business call is a treasure trove of valuable information.
For a developer building a voice application, this creates a profound and non-negotiable responsibility: the absolute, unwavering requirement to protect this data in transit. This is where the security features of a modern voice API for developers become not just a feature, but the very foundation of trust.
The threats are real, sophisticated, and ever-present. A compromised voice stream can lead to catastrophic data breaches, massive regulatory fines, and irreparable damage to a brand’s reputation. For any business deploying a voice application, enterprise voice security is not an optional add-on; it is a core, architectural prerequisite.
A modern voice API for developers is designed to solve this problem, providing a powerful, multi-layered security framework that allows developers to build applications with encrypted voice calls and secure voice streaming API capabilities by design. This guide will provide a deep dive into the threats and the essential technologies a developer must use to stream audio safely.
Table of contents
The Threat Model: What Are You Protecting Your Audio From?
To build an effective defense, you must first understand the adversary. The threats against a real-time audio stream are aimed at compromising its confidentiality and its integrity.
The Threat to Confidentiality: Eavesdropping and Man-in-the-Middle (MitM) Attacks
This is the most direct and classic threat.
- The Attack: A malicious actor positions themselves on the network path between the two ends of a call (e.g., on a public Wi-Fi network or by compromising a network router). They can then “sniff” the data packets that are flowing between the parties.
- The Risk: If the audio stream is not encrypted, the attacker can capture these packets, reassemble them, and listen to the entire conversation as if they were on the line. This is a massive privacy and data breach.
The Threat to Integrity: Packet Injection and Manipulation
This is a more subtle but equally dangerous threat.
- The Attack: An attacker who has intercepted the stream can do more than just listen. They can attempt to alter the packets in transit or to inject their own malicious packets into the stream.
- The Risk: While more difficult to execute, a successful integrity attack could theoretically be used to alter the content of a conversation, for example, to change the details of a financial transaction. More commonly, it can be used to disrupt the call and degrade the service quality.
Also Read: How Can Building Voice Bots Improve Customer Experience Across Channels?
The Solution: A Multi-Layered Encryption Strategy
A modern voice API for developers provides a comprehensive, multi-layered security model that is designed to protect every part of the voice communication lifecycle. The core of this strategy is end-to-end encryption. This is not a single technology but a powerful combination of two distinct encryption protocols that must work in tandem.
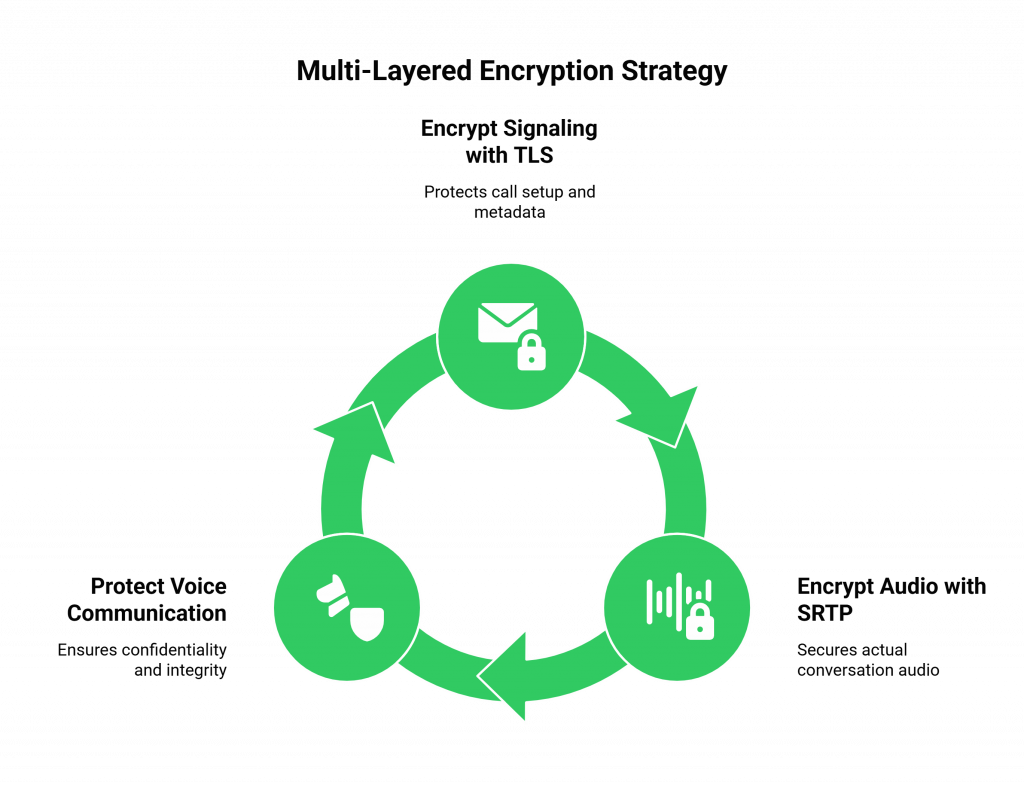
Layer 1: Encrypting the “Envelope” with Transport Layer Security (TLS)
The first layer of defense is to protect the signaling of the call. The signaling is the “conversation about the conversation.” It is the data that is used to set up, manage, and tear down the call.
- What It Is: TLS is the same, battle-hardened encryption protocol that is used to secure website traffic (HTTPS).
- What It Protects: A modern programmable voice api will use TLS to encrypt all of the API calls and webhook notifications between your application server and the voice platform. It will also use it to encrypt the low-level SIP signaling. This protects the metadata of the call, who is calling whom, the call duration, and the call control commands.
- Why It Matters: Without TLS, an attacker could see your call patterns or even attempt to hijack the call session.
Layer 2: Encrypting the “Content” with Secure Real-time Transport Protocol (SRTP)
This is the second, and most critical, layer for protecting the audio itself.
- What It Is: SRTP is a secure extension of the standard RTP protocol that is used to carry real-time media.
- What It Protects: SRTP encrypts the actual payload of the RTP packets, the audio data of your conversation. This is the core of a secure voice streaming API. It makes the live audio stream completely unintelligible to anyone who might intercept it.
- Why It Matters: Without SRTP, an attacker can perform an eavesdropping attack and listen to your entire conversation. With SRTP, all they can capture is a stream of meaningless, encrypted gibberish. This is the foundation of encrypted voice calls.
This table provides a clear summary of the two essential encryption layers.
| Encryption Protocol | What It Secures | Analogy | The Threat It Prevents |
| TLS (Transport Layer Security) | The call signaling and API communication. | The secure, opaque envelope of a letter. | An attacker cannot see who the letter is from or to, or tamper with the delivery instructions. |
| SRTP (Secure Real-time Transport Protocol) | The real-time audio media stream itself. | The content of the letter, written in an unbreakable code. | An attacker who steals the letter cannot read the confidential message inside. |
Ready to build your voice application on a platform that was architected with a security-first mindset from day one? Sign up for FreJun AI
Also Read: How Should QA Teams Evaluate Interactions While Building Voice Bots For Users?
How Does a Developer Implement This Securely?
A key benefit of a modern, developer-first voice api for developers is that it makes implementing this robust security incredibly simple. The platform does the heavy lifting of the complex cryptographic key exchanges and protocol management. The developer’s job is to simply “flip the switch” and enable these security features.
The Developer’s Security Checklist
- Always Use HTTPS for Your Webhooks and APIs: This ensures that all the communication between your application and the voice platform is encrypted with TLS. A good provider will enforce this.
- Enable Secure SIP (SIP over TLS): When you are configuring your connection to the voice platform (if you are using a SIP-based connection), you must choose the TLS option. This tells the system to encrypt all the SIP signaling.
- Explicitly Enable SRTP for Your Calls: This is the most important step. In your application’s code, when you initiate or configure a call via the API, you must include the parameter that explicitly enables SRTP. A high-quality provider like FreJun AI makes this as simple as setting a single flag in your API call.
- Securely Manage Your API Keys: This is a crucial part of the shared responsibility model. Your primary API keys and authentication tokens are the “keys to the kingdom.” They must be stored securely on your backend server and never, ever be exposed in your client-side (web or mobile) application’s code.
What is FreJun AI’s Commitment to Enterprise Voice Security?
At FreJun AI, we understand that for our enterprise customers, security is not just a feature; it is the foundation of trust. Our Teler voice platform was built from the ground up with a security-first architectural philosophy.
- Encryption by Default: We believe that security should be the default, not an option. Our voice API for developers is designed to make it as simple as possible to enable end-to-end encryption for every call.
- A Hardened, Global Infrastructure: Our globally distributed infrastructure is protected by multiple layers of network security, including DoS/DDoS mitigation, and is hosted in high-security, SOC 2 and ISO 27001 compliant data centers.
- A Foundation for Compliance: Our platform is designed to provide the tools and the security posture that our customers need to build applications that are compliant with regulations like HIPAA and GDPR. This is our core promise: “We handle the complex voice infrastructure so you can focus on building your AI securely.”
Also Read: How Can Small Teams Start Building Voice Bots With Minimal Cost?
Conclusion
In the modern digital landscape, the voice call is a powerful and valuable source of data. But with this value comes the profound responsibility to protect it. For a developer using a voice API for developers, building a secure application is not an optional extra; it is a core professional and ethical obligation.
The good news is that a modern, enterprise-grade voice API provides a powerful and easy-to-use set of tools to achieve this.
By understanding and correctly implementing a multi-layered security strategy, centered around the powerful duo of TLS and SRTP, developers can confidently build the next generation of voice applications, ensuring that every conversation is not just intelligent, but also completely private and secure.
Have specific security or compliance requirements for your enterprise voice application? Schedule a demo for FreJun Teler.
Also Read: How to Set Up IVR Software for Your Call Center (Step-by-Step Guide)
Frequently Asked questions (FAQs)
End-to-end encryption, using both TLS for signaling and SRTP for the media stream, is the single most critical security feature.
A secure voice streaming api is one that uses the Secure Real-time Transport Protocol (SRTP) to encrypt the raw audio of a call, protecting it from eavesdropping.
Encrypted voice calls protect the entire communication, including setup information and the conversation itself, using strong cryptographic protocols.
Enterprise voice security involves a much more rigorous, multi-layered approach that includes not just encryption, but also strong authentication, regulatory compliance, and a hardened infrastructure.
TLS encrypts the call setup and control messages. SRTP encrypts the actual audio packets of the conversation. You need both for complete protection.
It is an attack where a malicious actor secretly intercepts the communication between two parties. Strong encryption (TLS/SRTP) is the primary defense against this.
Store your secret API keys only on your secure backend server and never expose them in your client-side (web or mobile) code.