Imagine you are building a banking app. You would never dream of sending a user’s password over the internet in plain text. You would lock it down with layers of encryption and security protocols.
Now imagine that same user clicks a “Call Support” button in your app. They start telling the agent their mother’s maiden name or the last four digits of their social security number. Is that voice call just as secure as the password was?
In many applications the answer is shockingly no.
Voice data is often the “forgotten” data. Developers focus heavily on securing databases and web forms but they sometimes leave the voice stream wide open. This exposes businesses to massive risks including eavesdropping and toll fraud and compliance violations.
To build a safe application you need a voice calling API and SDK that prioritizes security from the ground up. You need to understand how to lock the front door (authentication) and how to armor the transport truck (encryption).
In this guide we will explore exactly what secures a production voice system. We will look at the layers of defense required for a compliant voice SDK and how to prevent fraud and how infrastructure platforms like FreJun AI provide the secure foundation necessary for enterprise grade communication.
Table of contents
- Why Is Voice Security Often Overlooked?
- What Are the Core Threats to Voice Systems?
- How Does Encryption Protect the Conversation?
- What Is a Compliant Voice SDK?
- How Do You Authenticate Users Effectively?
- What Role Does Infrastructure Play in Security?
- How Do You Ensure Audit Ready Calls?
- Why Is a Regulated Calling API Essential?
- Comparison: Insecure vs. Secure Implementation
- How to Implement Security Best Practices
- Conclusion
- Frequently Asked Questions (FAQs)
Why Is Voice Security Often Overlooked?
Voice feels fleeting. When you speak the words disappear into the air. Because of this many developers treat voice data differently than text data. They assume that because it is real time it is harder to steal.
This is a dangerous myth.
Voice over IP (VoIP) breaks your voice down into digital packets. These packets travel over the public internet just like emails or web pages. If they are not encrypted a hacker sitting on the same Wi-Fi network or a compromised router can intercept these packets. They can reassemble them and listen to the entire conversation later.
Furthermore voice systems are a target for financial theft. Hackers attack phone systems to commit “toll fraud.” They hijack your phone lines to pump traffic to expensive premium rate numbers in other countries leaving you with a bill for thousands of dollars.
What Are the Core Threats to Voice Systems?
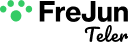
To defend your castle you must know your enemy. When you integrate a voice calling API and SDK you are exposing your app to three main types of attacks.
1. Eavesdropping (Man in the Middle)
This is the spy movie scenario. An attacker intercepts the audio stream between the caller and the server. If the stream is not encrypted they can listen to sensitive details like credit card numbers or health information.
2. Identity Spoofing
This is when a bad actor pretends to be a legitimate user. They might manipulate the data packets to make it look like a call is coming from your CEO or your bank. This destroys trust and facilitates social engineering attacks.
3. Denial of Service (DoS)
Voice systems rely on real time processing. Attackers know this. They flood your system with thousands of fake call initiation requests. This overwhelms your server causing it to crash and denying service to your actual customers.
Also Read: How Programmable SIP Improves Voice Quality and Latency for AI-Powered Calls?
How Does Encryption Protect the Conversation?
The primary defense against eavesdropping is encryption. A secure voice calling API and SDK handles this using two specific protocols.
SIP over TLS (Securing the Envelope)
SIP (Session Initiation Protocol) is the language used to set up a call. It says “User A wants to call User B.”
If you send this in plain text an attacker knows exactly who is talking to whom.
TLS (Transport Layer Security) encrypts this signaling data. It is like putting the letter in a steel envelope. The postman (the internet) delivers it but cannot read the address or the instructions on the outside.
SRTP (Securing the Letter)
Once the call is set up the actual voice audio flows via RTP (Real time Transport Protocol).
Secure RTP (SRTP) encrypts the audio payload itself. Even if a hacker intercepts the packets all they see is scrambled noise. They cannot decode it back into speech without the digital key.
FreJun AI enforces these standards by default. We handle the complex voice infrastructure so you can focus on building your AI. When you use our platform we ensure that media streams are encrypted protecting your user conversations from prying ears.
What Is a Compliant Voice SDK?
If you work in healthcare or finance security is not just a good idea. It is the law.
A compliant voice SDK is built to adhere to strict industry regulations.
- HIPAA (Healthcare): If a patient discusses a diagnosis over your app that audio is Protected Health Information (PHI). The system must ensure that data is encrypted and access is strictly controlled.
- PCI-DSS (Finance): If a user reads a credit card number the system must ensure that this audio is not stored in an insecure way.
- GDPR (Europe): You must be able to delete user data upon request.
Building compliance from scratch is difficult. You have to prove to auditors that your encryption keys are rotated and your logs are secure.
Using a platform like FreJun simplifies this. We act as a secure transport layer. We transmit the data securely without storing it unnecessarily. This helps developers build applications that meet these rigorous standards without becoming security engineers themselves.
How Do You Authenticate Users Effectively?
Encryption protects the data while it moves. Authentication protects access to the data.
A common mistake developers make is hardcoding API keys into their mobile apps. If a hacker decompiles your app they find the key. Now they can make calls using your account and your money.
The Token Based Approach
A secure voice calling API and SDK uses short lived tokens (like JSON Web Tokens or JWTs).
- Login: The user logs into your app using their username and password.
- Request: Your app asks your backend server for a “Voice Token.”
- Grant: Your backend server (which holds the secret API keys) generates a temporary token valid for only one hour and sends it to the app.
- Connect: The app uses this token to connect to the FreJun voice cloud.
If a hacker steals this token it expires quickly reducing the damage. FreJun provides robust authentication SDKs to handle this token exchange seamless making it easy to implement best practices.
Ready to build a secure voice application? Sign up for FreJun AI to get your API keys and access our security documentation.
What Role Does Infrastructure Play in Security?
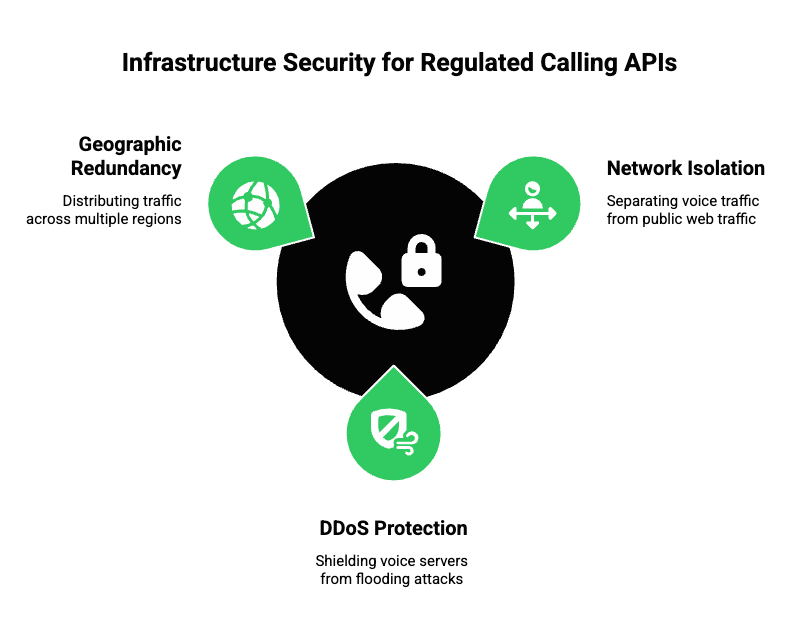
You can write secure code but if the server it runs on is weak you are still vulnerable. Infrastructure security is the foundation of a regulated calling API.
This is where FreJun Teler shines. Teler is our telephony infrastructure arm that provides elastic SIP trunking.
Network Isolation
FreJun isolate voice traffic. We do not mix your voice packets with public web traffic on the same unmanaged routes. We prioritize secure direct interconnects with carriers. This reduces the number of “hops” the data takes across the public internet reducing the attack surface.
DDoS Protection
Voice servers are prone to flooding attacks. FreJun’s distributed infrastructure acts as a shield. We have automated systems that detect traffic spikes. If a bad actor tries to flood your phone lines our system identifies the pattern and blocks the malicious IP addresses instantly while letting legitimate calls through.
Geographic Redundancy
If a data center is attacked or goes offline for physical reasons (like a power outage) your voice system needs to stay up. FreJun distributes traffic across multiple global regions. This redundancy ensures that your business communication remains active even during a crisis.
Also Read: Why Startups Are Switching to Programmable SIP for Scalable Voice AI?
How Do You Ensure Audit Ready Calls?
For enterprise companies “trust me” is not enough. You need proof.
Audit-ready calls mean that every interaction is logged and traceable. If a dispute arises six months from now you need to be able to pull the record.
A secure system provides:
- Detailed Logs: Who called whom and when and for how long.
- Immutable Recordings: If you record calls the files must be stored in a “Write Once Read Many” (WORM) format. This means nobody not even an admin can alter the recording file after it is saved.
- Access Trails: A log of exactly which employee listened to a recording.
FreJun allows developers to access detailed metadata for every call. We provide the transparency needed to satisfy internal compliance teams and external auditors.
Why Is a Regulated Calling API Essential?
The telephone network is highly regulated. Governments are cracking down on spam calls and spoofing.
In the United States the FCC implemented a framework called STIR/SHAKEN. This is a technology that verifies caller IDs. It is like a digital signature for phone calls.
If you use a cheap non-compliant provider your calls might be flagged as “Spam Risk” on your customer’s phone. This kills your answer rates.
A regulated calling API like FreJun participates in these trust frameworks. We ensure that your calls are signed correctly. This tells the receiving carrier “This call is really from Business X.” It protects your brand reputation and ensures your legitimate calls get answered.
Comparison: Insecure vs. Secure Implementation
Here is a quick look at the difference between a risky setup and a professional one.
| Feature | Insecure Implementation | Secure Implementation (FreJun) |
| Signaling | Plain Text (SIP) | Encrypted (SIP over TLS) |
| Media | Plain Audio (RTP) | Encrypted (SRTP) |
| Auth | Hardcoded API Keys | Short-lived Access Tokens |
| Storage | Public S3 Buckets | Encrypted Private Storage |
| Compliance | None | HIPAA/GDPR Ready Architecture |
| Network | Public Internet Only | Optimized/Isolated Routes |
| Identity | Unverified Caller ID | Signed (STIR/SHAKEN) |
How to Implement Security Best Practices
If you are a developer integrating a voice calling API and SDK here is your security checklist.
1. Rotate Your Keys
Never keep the same API keys forever. Rotate them regularly. FreJun’s dashboard makes it easy to generate new keys and revoke old ones if you suspect a leak.
2. Validate Input
Never trust data coming from the client. If the app sends a phone number validate it on your backend before dialing. This prevents “injection” attacks where hackers try to manipulate the dialing string.
3. Least Privilege
Give your agents only the access they need. A junior support rep should not be able to delete call recordings. Use role based access control (RBAC) in your application.
4. Monitor for Anomalies
Set up alerts. If a single user makes 500 calls in one hour that is suspicious. It might be a bot. Catching these patterns early saves money and protects your system.
Also Read: The Role of Programmable SIP in Next-Gen Customer Support Automation
Conclusion
Security is not a feature you add at the end. It is a mindset you start with.
When building a voice application you are responsible for the most human form of data there is: the human voice. Protecting that data prevents fraud and ensures compliance and builds trust with your users.
Using a robust voice calling API and SDK is the most effective way to secure your production system. You do not need to be a cryptography expert. You just need to choose a partner that builds security into the DNA of the platform.
FreJun AI provides that foundation. With FreJun Teler providing secure elastic SIP trunking and our SDKs enforcing encryption and authentication by default we make it easy to build audit-ready calls. We handle the heavy lifting of security infrastructure so you can sleep soundly knowing your conversations are safe.
Want to discuss your specific security requirements? Schedule a demo with our team at FreJun Teler and let us help you architect a safe and compliant voice solution.
Also Read: Create High-Impact WhatsApp Message Templates for Enterprises in Dubai
Frequently Asked Questions (FAQs)
SIP is the standard protocol for setting up calls but it sends data in plain text. SIPS (Secure SIP) uses TLS to encrypt that data. It is the difference between sending a postcard and sending a sealed letter.
No. We respect privacy. Recording is an optional feature that you must enable via the API. If you do enable it the recordings are stored securely.
Toll fraud is when hackers gain access to your phone system and make expensive international calls to numbers they own effectively stealing money from your account.
A token is generated on your secure server. It grants permission for one specific user to make calls for a limited time. If a hacker tries to make a call without a valid token the FreJun cloud rejects it immediately.
Not necessarily. While VoIP travels over the internet which has risks modern encryption (SRTP/TLS) makes it extremely difficult to intercept. In many ways it is more secure than old copper wires which could be physically tapped.
It means the software development kit provides the tools (like encryption and logging) necessary for you to build an app that meets laws like HIPAA or GDPR.
Yes. Our infrastructure supports the high levels of security and encryption required for financial services applications ensuring sensitive customer data is protected.
It is a set of protocols used in the US and Canada to verify that the calling number is legitimate. It prevents scammers from spoofing (faking) phone numbers.