Imagine you own a very expensive and fast sports car. You would not just leave the keys in the ignition with the doors wide open. If you did that anyone could jump in and drive it recklessly. They could speed through school zones or crash into other cars. Even though you were not driving you would be the one responsible for the damage because you owned the car.
Building a voice application is very similar. When you connect your software to the global telephone network you are accessing a powerful tool. You can make calls to millions of people instantly. If you do not protect this access bad actors could use your system to send spam or harass people or commit fraud. This could lead to massive fines and lawsuits.
This is where the AI Voice API Key comes in. It is more than just a password. It is a smart digital license that controls exactly who can drive your car and where they can go and how fast they are allowed to travel.
In this article we will explore how this small string of code acts as a powerful compliance officer. We will look at how it handles voice API security and prevents abuse and ensures that your business stays on the right side of the law. We will also see how infrastructure platforms like FreJun AI use these keys to provide a safe foundation for your voice applications.
Table of contents
- What Is the True Function of an AI Voice API Key?
- Why Is Voice Compliance a Major Business Risk?
- How Does the Key Enable Voice API Security?
- Can an API Key Stop Spam and Robocalls?
- How Do Keys Prevent Unauthorized Call Prevention?
- How Does FreJun Teler Use Keys for Identity Verification?
- How Does Geofencing Work with API Keys?
- Why Is Audit Logging Essential for Legal Defense?
- How Does FreJun AI Simplify Compliance for Developers?
- How to Manage Your Keys Effectively?
- Conclusion
- Frequently Asked Questions (FAQs)
What Is the True Function of an AI Voice API Key?
Most developers think of an API key as a simple login tool. You send the key and the server lets you in. However in the world of telecom compliance the key does much more.
An AI Voice API Key is a unique identifier that links every single request to a specific account and a specific set of rules. It is the central point of control.
When your application tries to make a call it sends the key to the provider. The provider checks the key against a database of policies.
- Is this key active?
- Does this key have permission to make international calls?
- Has this key exceeded its daily limit?
If the answer to any of these questions is “wrong” the provider blocks the call immediately. This happens in milliseconds. By using this mechanism companies can enforce strict internal and external compliance rules without needing a human manager to approve every dial.
Why Is Voice Compliance a Major Business Risk?
You might wonder why we need such strict controls. The answer is simple. The penalties for messing up are huge.
Governments around the world are cracking down on spam calls and robocalls. In the United States the Telephone Consumer Protection Act (TCPA) allows individuals to sue companies for up to $1,500 for every single unwanted call. If your system is hacked and makes 1,000 bad calls you could owe $1.5 million instantly.
According to the Federal Communications Commission (FCC) record breaking fines have been issued to companies that failed to control their calling traffic. In one instance telemarketers were fined $225 million for making spoofed robocalls.
Beyond the money there is reputation. If your business phone number gets flagged as “Spam” on people’s cell phones nobody will answer your calls anymore. An AI Voice API Key is your first line of defense against these disasters.
Also Read: What Should Developers Expect from a Voice API for Developers in 2026?
How Does the Key Enable Voice API Security?
The most basic function of the key is authentication. This is how the system knows you are you.
In a secure setup the API key is a long string of random characters. It is impossible to guess. When you Sign up for FreJun AI you receive this secret key.
You must keep it safe. You should never publish it in public code repositories like GitHub. If a hacker finds your key they can pretend to be you.
However modern voice API security goes further. It allows for “IP Allowlisting.” This means you can tell the voice provider to only accept the API key if the request comes from your specific computer server. If a hacker steals your key but tries to use it from their own computer the system will reject it. This two layer protection ensures that even if the key is leaked the system remains secure.
Can an API Key Stop Spam and Robocalls?
One of the biggest compliance risks is volume. Legitimate businesses rarely make 100 calls in one second. Scammers do.
This is where abuse protection comes into play. The API key is attached to a “Rate Limit.” This is a rule that says “This key can only make 5 calls per second.”
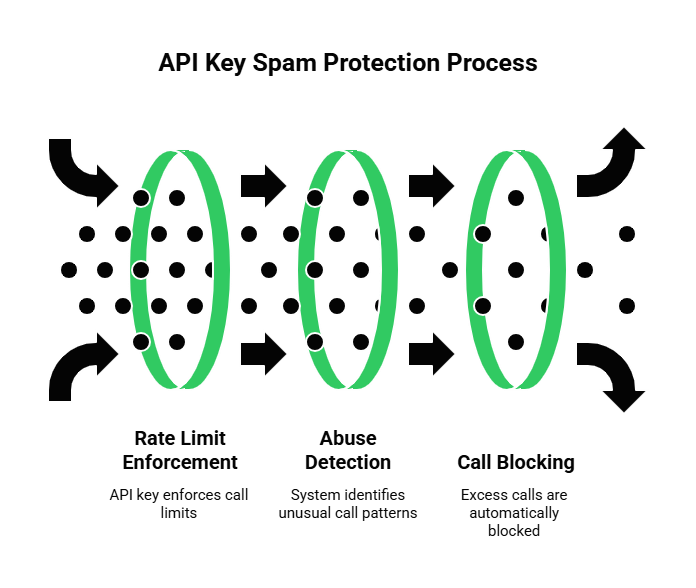
If your software has a bug and starts dialing wildly the API key will hit the limit. The infrastructure provider will block the excess calls automatically. This acts like a circuit breaker in your house. It stops the flow of electricity before the house burns down.
FreJun AI implements these smart limits to protect our customers. We handle the complex voice infrastructure so you can focus on building your AI. By monitoring the traffic on each key we can detect unusual spikes that look like spam attacks and shut them down before they cause regulatory issues for you.
How Do Keys Prevent Unauthorized Call Prevention?
In a large company you might have different teams. The sales team needs to make outbound calls. The support team only needs to receive inbound calls. You do not want a junior developer on the support team to accidentally write a script that calls a thousand customers.
You can solve this by issuing different API keys with different “Scopes” or permissions.
- Key A (Sales): Can make calls. Can record calls.
- Key B (Support): Can only fetch call logs. Cannot make calls.
This strategy is known as unauthorized call prevention. By limiting what each key can do you minimize the blast radius if a mistake happens.
Here is a comparison of a system without these controls versus one with API key enforcement.
| Feature | Without API Key Controls | With AI Voice API Key Policies |
| Access Level | Open to anyone with the password | Granular permissions per team |
| Volume Control | Unlimited calling (Dangerous) | Strict rate limits (Safe) |
| ** Geographic Reach** | Can call anywhere globally | Locked to specific countries |
| Cost Control | Unpredictable bills | Set budget caps |
| Security | Single point of failure | IP restricted access |
| Audit Trail | Hard to track who did what | precise logs for every request |
How Does FreJun Teler Use Keys for Identity Verification?
Compliance is not just about stopping bad calls. It is also about ensuring good calls get through.
In the modern telephone network there is a framework called STIR/SHAKEN. This is a fancy way of saying “Caller ID Verification.” It stops scammers from faking their phone numbers.
When you make a call using FreJun Teler your AI Voice API Key proves your identity to us. Because we know who you are we can digitally sign your call. This tells the receiving phone carrier “We verified this caller. They are legitimate.”
This results in your calls showing up as “Verified” on the customer’s phone rather than “Spam Likely.” This is a massive advantage for legitimate businesses.
Also Read: How Can a Voice API for Developers Reduce Telephony Complexity?
How Does Geofencing Work with API Keys?
Different countries have different laws. In Germany you cannot record a call without two way consent. In some countries marketing calls are strictly banned at night.
Your AI Voice API Key can be configured with geographic rules. This is called Geofencing.
You can set a policy that says “This key can only call numbers in the United States and Canada.” If your AI tries to dial a number in North Korea or a high fraud region the API will reject the request.
This prevents accidental compliance violations. It also saves you money. International fraud is a common attack where hackers use your account to call expensive premium rate numbers in remote islands. By locking your key to your target regions you eliminate this risk entirely.
Why Is Audit Logging Essential for Legal Defense?
Imagine a scenario where a consumer claims you called them illegally. They threaten to sue you. How do you prove you followed the rules?
Your AI Voice API Key creates a paper trail. Every time the key is used the voice provider creates a log entry.
- Timestamp: 10:00 AM
- Key ID: ABC-123
- Action: Dialed 555-0199
- Result: Connected
These logs are immutable. They cannot be change. In a legal dispute these logs are your evidence. You can prove that you only called the customer after they submitted a form or that you stopped calling when they asked you to.
According to a cybersecurity report by IBM the average cost of a data breach is over $4 million. However having extensive logging and incident response plans can reduce this cost significantly. Detailed API logs allow you to detect a breach early and prove exactly what data was or was not access.
How Does FreJun AI Simplify Compliance for Developers?
Dealing with telecom laws is hard. You have to worry about the TCPA and GDPR and carrier regulations. It is a headache for developers who just want to build a cool voice agent.
FreJun AI abstracts this complexity away. We bake compliance into our infrastructure.
When you use our platform you leverage our abuse protection systems.
- FreJun Teler handles the elastic SIP trunking and ensures that your signaling data is compliant with carrier standards.
- Our API gateways enforce the rate limits and geographic blocks associated with your key.
This means you do not have to write code to check if a number is valid or if you are calling too fast. Our infrastructure checks it for you. You just send the request with your key and we handle the safety checks.
How to Manage Your Keys Effectively?
To get the most out of this system you need to manage your keys properly. Here are three best practices.
1. Rotate Your Keys
Do not use the same key forever. Change it every few months. This ensures that if an old employee took a key with them it stops working.
2. Use Environment Variables
Never write your key directly into your code. Store it in a secure environment variable on your server. This prevents it from being accidentally uploaded to the internet.
3. Monitor Your Usage
Check your dashboard regularly. If you see your key being used at 3:00 AM when your office is close investigate immediately.
Also Read: How Does a Voice API for Developers Support Web and Mobile Voice Apps?
Conclusion
The AI Voice API Key is the unsung hero of the modern voice application. It is the gatekeeper. It ensures that your powerful AI technology is used responsibly and legally.
By enforcing authentication and rate limits and geographic boundaries the key protects your business from hackers and lawsuits. It enables voice API security by ensuring that only authorized personnel can initiate calls. It provides unauthorized call prevention by limiting scopes. And it offers abuse protection by stopping spam spikes before they happen.
However these features are only effective if you use a robust infrastructure partner. FreJun AI provides the secure and compliant foundation you need. We handle the heavy lifting of telecom regulation and security so you can focus on creating amazing voice experiences for your customers.
With granular API key controls and the power of FreJun Teler you can deploy your voice agents with confidence knowing that your compliance guardrails are always active.
Ready to secure your voice operations? Schedule a demo with our team at FreJun Teler and let us show you how to build a safe and compliant voice stack.
Also Read: UK Phone Number Formats for UAE Businesses
Frequently Asked Questions (FAQs)
An AI Voice API Key is a secure code used to authenticate requests between your application and a voice provider. It acts like a digital ID card that enforces security and compliance rules.
The key is linked to a rate limit. If an application tries to make too many calls in a short period the system detects this as potential spam and blocks the excess calls automatically.
You can but it is not recommended. It is better to create separate keys for different functions like one for development and one for production to minimize risk.
If a hacker gets your key they can make calls on your account. You should immediately delete the compromised key in your dashboard and issue a new one to stop the unauthorized access.
FreJun uses industry standard encryption to validate keys. We also allow you to restrict key usage to specific IP addresses adding an extra layer of security.
Yes. The key authenticates your account which allows FreJun to sign your calls with STIR/SHAKEN protocols. This helps your calls appear as verified on the recipient’s phone.
Yes. You can configure your API key settings to only allow calls to specific countries. This prevents accidental spending on expensive international routes.
Logs provide proof of your actions. If a regulator questions your calling practices the logs linked to your API key show exactly when and why you made each call.